
H12-721 Exam Questions & Answers
Exam Code: H12-721
Exam Name: HCIP-Security-CISN V3.0
Updated: Nov 03, 2023
Q&As: 65
At Passcerty.com, we pride ourselves on the comprehensive nature of our H12-721 exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free Huawei H12-721 Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your Huawei H12-721 exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free Huawei H12-721 Dumps
Practice These Free Questions and Answers to Pass the Huawei Certification Exam
The USG series product dual-system hot backup does not involve the ______ protocol.
A. HRP
B. VRRP
C. VGMP
D. IGMP
In the attack shown below, a victim host packet captures the traffic. According to the information shown, what kind of attack is this?
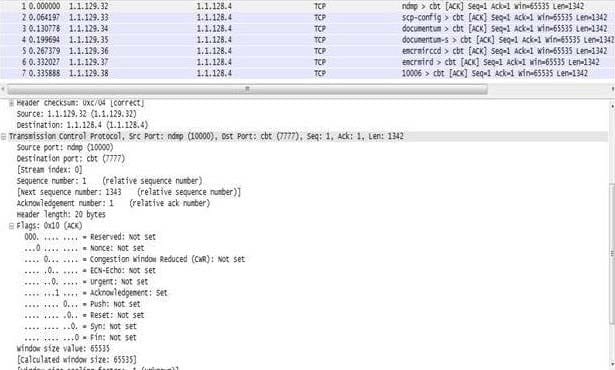
A. SYN Flood
B. SYN-ACK Flood
C. ACK-Flood
D. Connection Flood
A man in the middle attack refers to an intermediate that sees the data exchange between server and client. To the server, all messages appear to be sent to or received from the client; and to the client all the packets appear to have been sent to or received from the server. If a hacker is using the man-in-the-middle attack, the hacker will send at least two data packets as shown to achieve this attack.
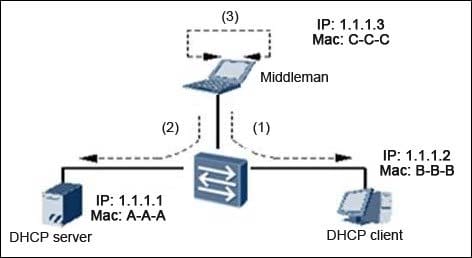
Which of the following packet 1 and packet 2 Field Description is correct? (Choose two answers)
A. Packet 1: Source IP 1.1.1.1 Source MAC C-C-C
The purpose of IP 1.1.1.2
The purpose of Mac B-B-B
B. Packet 1: Source IP 1.1.1.3 Source MAC C-C-C The purpose of IP 1.1.1.2 The purpose of Mac B-B-B
C. Packet 2: Source IP 1.1.1.2 Source MAC C-C-C The purpose of IP 1.1.1.1 The purpose of Mac A-A-A
D. Packet 2: Source IP 1.1.1.3 Source MAC C-C-C The purpose of IP 1.1.1.1 The purpose of Mac A-A-A
An enterprise network cutover has just been done. The old network equipment is off the assembly line and the line is now on new network equipment. After operational testing we found that the majority of traffic will not work.
What will be administrators quickest way to restore business?
A. stratification
B. Break Law
C. substitution method
D. Block Method
What do we want to achieve with Virtual firewalls on a single physical firewall device where we create virtual multiple logical firewalls and multiple instances? (Choose three answers)
A. Security multiple instances
B. VPN multi-instance
C. configure multiple instances
D. exchange multiple instances
Viewing Page 1 of 3 pages. Download PDF or Software version with 65 questions

