
JN0-412 Exam Questions & Answers
Exam Code: JN0-412
Exam Name: Cloud, Specialist (JNCIS-Cloud)
Updated: Nov 11, 2024
Q&As: 65
At Passcerty.com, we pride ourselves on the comprehensive nature of our JN0-412 exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free Juniper JN0-412 Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your Juniper JN0-412 exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free Juniper JN0-412 Dumps
Practice These Free Questions and Answers to Pass the JNCIS-Cloud Exam
Which SDN solution allows the control plane to remain on legacy hardware as a stop-gap measure until you are ready to replace the current hardware?
A. SDN using NVGRE
B. SDN as an overlay
C. SDN using an API
D. open SDN
Which two statements about Kubernetes clusters are correct? (Choose two.)
A. The master coordinates the cluster.
B. The minions are responsible for running the applications.
C. The nodes are responsible for running the applications.
D. The pod controller coordinates the cluster.
When creating a firewall rule in Contrail Security, which two types of endpoints are available? (Choose two.)
A. virtual network
B. tag
C. domain
D. service level
Which statements correct about Contrail security?
A. Contrail security is used to control access into Junos devices.
B. Contrail security is used to apply security features and segment traffic flows.
C. Contrail security is used to analyze network performance and learn traffic patterns.
D. Contrail security is used to control management access to VNFs.
Click the Exhibit button.
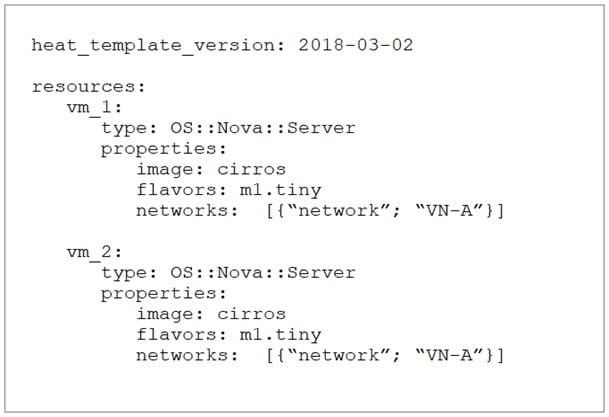
What will be the result of deploying the Heat template shown in the exhibit?
A. Neither VM will be deployed.
B. Only vm_2 will be deployed and vm_1 will be overwritten.
C. Both vm_1 and vm_2 will be deployed.
D. Only vm_1 will be deployed and vm_2 will fail.
Viewing Page 1 of 3 pages. Download PDF or Software version with 65 questions

