PCCET Exam Questions & Answers
Exam Code: PCCET
Exam Name: Palo Alto Networks Certified Cybersecurity Entry-level Technician
Updated:
Q&As: 200
At Passcerty.com, we pride ourselves on the comprehensive nature of our PCCET exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free Palo Alto Networks PCCET Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your Palo Alto Networks PCCET exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free Palo Alto Networks PCCET Dumps
Practice These Free Questions and Answers to Pass the Certified Cybersecurity Associate Exam
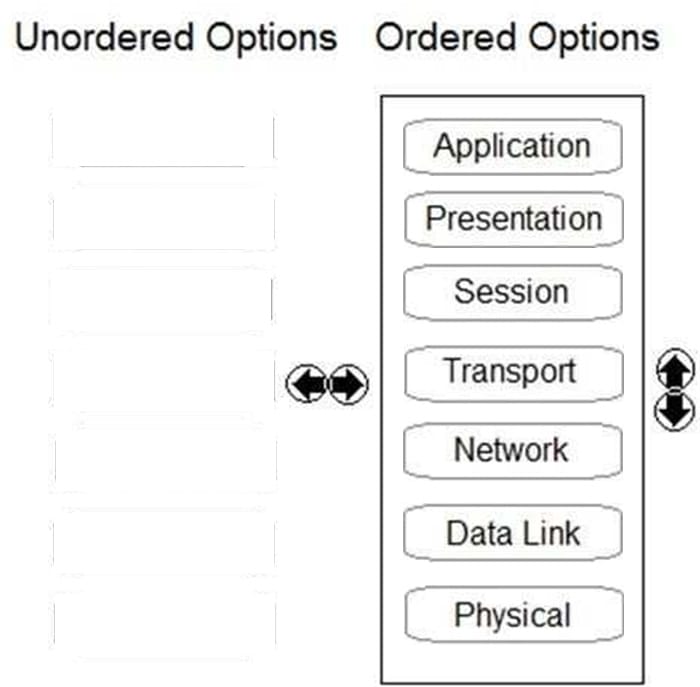
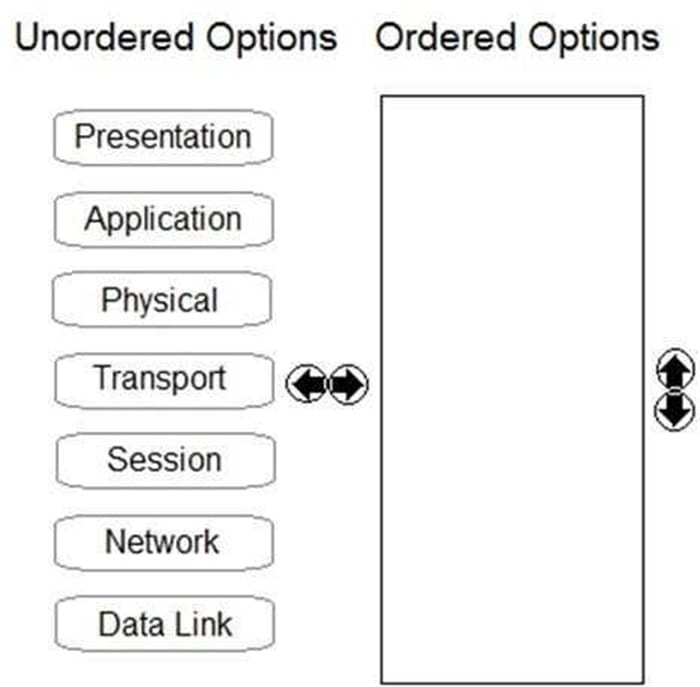
DRAG DROP
Order the OSI model with Layer7 at the top and Layer1 at the bottom.
Select and Place:
Which Palo Alto Networks tools enable a proactive, prevention-based approach to network automation that accelerates security analysis?
A. MineMeld
B. AutoFocus
C. WildFire
D. Cortex XDR
In which phase of the cyberattack lifecycle do attackers establish encrypted communication channels back to servers across the internet so that they can modify their attack objectives and methods?
A. exploitation
B. actions on the objective
C. command and control
D. installation
Which not-for-profit organization maintains the common vulnerability exposure catalog that is available through their public website?
A. Department of Homeland Security
B. MITRE
C. Office of Cyber Security and Information Assurance
D. Cybersecurity Vulnerability Research Center
What does SOAR technology use to automate and coordinate workflows?
A. algorithms
B. Cloud Access Security Broker
C. Security Incident and Event Management
D. playbooks
Viewing Page 1 of 3 pages. Download PDF or Software version with 200 questions