PCCSA Exam Questions & Answers
Exam Code: PCCSA
Exam Name: Palo Alto Networks Certified Cybersecurity Associate
Updated: Dec 17, 2024
Q&As: 79
At Passcerty.com, we pride ourselves on the comprehensive nature of our PCCSA exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free Palo Alto Networks PCCSA Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your Palo Alto Networks PCCSA exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free Palo Alto Networks PCCSA Dumps
Practice These Free Questions and Answers to Pass the Palo Alto Certifications and Accreditations Exam
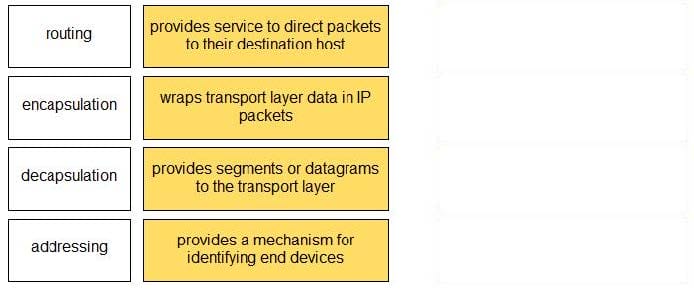
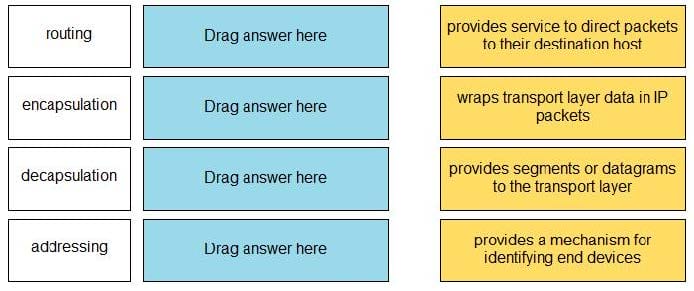
DRAG DROP
Match the OSI network model Layer 3 function to the correct description.
Select and Place:
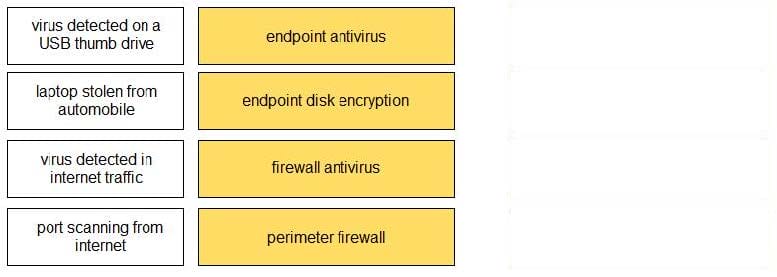
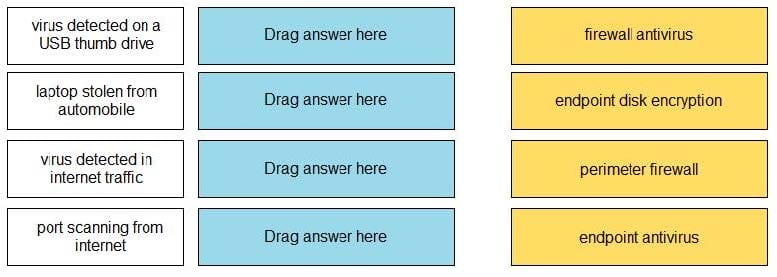
DRAG DROP
Match the attack definition to the type of security method used to protect against the attack.
Select and Place:
Company policy allows employees to access the internet. While searching for office supplies on the internet, a corporate user mistypes a URL, connects to a malicious website, and unknowingly downloads malware.
Which action should have been taken to prevent the malware download but still allow user access to the internet?
A. deploy a firewall with content filtering capabilities on the corporate perimeter
B. allow only encrypted HTTPS access to the internet
C. configure digital certificates for all users to authenticate internet downloads
D. permit web connections only to TCP port 443
Which two reconnaissance tools might an attacker use to scan for vulnerable network services and settings? (Choose two.)
A. bandwidth analyzer
B. intrusion detection
C. port scanner
D. password cracker
What is the result of deploying virtualization in your data center?
A. reduced security threat
B. reduced operational costs
C. increased hardware capital costs
D. increased host provisioning
Viewing Page 1 of 3 pages. Download PDF or Software version with 79 questions