
PT0-001 Exam Questions & Answers
Exam Code: PT0-001
Exam Name: CompTIA PenTest+ Exam
Updated: Apr 01, 2024
Q&As: 306
At Passcerty.com, we pride ourselves on the comprehensive nature of our PT0-001 exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free CompTIA PT0-001 Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your CompTIA PT0-001 exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free CompTIA PT0-001 Dumps
Practice These Free Questions and Answers to Pass the CompTIA PenTest+ Exam
Given the following Python script:
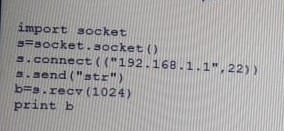
Which of the following actions will it perform?
A. ARP spoofing
B. Port scanner
C. Reverse shell
D. Banner grabbing
Given the following:
http://example.com/download.php?id-.../.../.../etc/passwd
Which of the following BEST describes the above attack?
A. Malicious file upload attack
B. Redirect attack
C. Directory traversal attack
D. Insecure direct object reference attack
An organization has requested that a penetration test be performed to determine if it is possible for an attacker to gain a foothold on the organization's server segment. During the assessment, the penetration tester identifies tools that appear to have been left behind by a prior attack. Which of the following actions should the penetration tester take?
A. Attempt to use the remnant tools to achieve persistence.
B. Document the presence of the left-behind tools in the report and proceed with the test.
C. Remove the tools from the affected systems before continuing on with the test.
D. Discontinue further testing and report the situation to management.
The scope of a penetration test requires the tester to be stealthy when performing port scans. Which of the following commands with Nmap BEST supports stealthy scanning?
A. -min-rate
B. -max-length
C. -host-timeout
D. -max-rate
Which of the following is the BEST way to deploy vulnerability scanners with many networks segmented by firewalls with active IPS rules?
A. Deploy a single scanner inside each network segment.
B. Deploy many scanners inside one segment and allow any rules.
C. Deploy one internal scanner and one external scanner.
D. Deploy one internal scanner with heavy server resources.
Viewing Page 1 of 3 pages. Download PDF or Software version with 306 questions

